Tag Archives: stuxnet
Report: Obama authorized a secret cyber operation against Russia
 President Barack Obama learned of Russia's attempts to hack US election systems in early August 2016, and as intelligence mounted over the following months, the White House deployed secrecy protocols it hadn't used since the 2011 raid on Osama bin La...
President Barack Obama learned of Russia's attempts to hack US election systems in early August 2016, and as intelligence mounted over the following months, the White House deployed secrecy protocols it hadn't used since the 2011 raid on Osama bin La...
Obama pardons Stuxnet leak source James Cartwright
 Chelsea Manning isn't the only source of online leaks to get a new lease on life. President Obama has pardoned General James Cartwright, who pleaded guilty to lying to the FBI when it investigated leaks that revealed details of Stuxnet, the US-backed...
Chelsea Manning isn't the only source of online leaks to get a new lease on life. President Obama has pardoned General James Cartwright, who pleaded guilty to lying to the FBI when it investigated leaks that revealed details of Stuxnet, the US-backed...
Researchers discover advanced cyber-espionage malware
 Both Kaspersky and Symantec have unearthed a new type of malware so advanced, they believe it could have links to a country's intelligence agency. They're calling it "Remsec," "Strider" (Aragorn's nickname in LOTR) and "ProjectSauron," because it has...
Both Kaspersky and Symantec have unearthed a new type of malware so advanced, they believe it could have links to a country's intelligence agency. They're calling it "Remsec," "Strider" (Aragorn's nickname in LOTR) and "ProjectSauron," because it has...
Alex Gibney on Stuxnet and why we need to talk about cyberwar
 It's been six years since we've discovered Stuxnet, the worm that infected Windows PCs worldwide, and was eventually traced to the US and Israel as a way to attack Iran's nuclear program. It was the first time a cyberweapon was used to attack a physi...
It's been six years since we've discovered Stuxnet, the worm that infected Windows PCs worldwide, and was eventually traced to the US and Israel as a way to attack Iran's nuclear program. It was the first time a cyberweapon was used to attack a physi...
Feds indict seven Iranians for hacking banks, NY state dam
 Just days after accusing Syrian hackers of a wide range of crimes, US Attorney General Loretta Lynch unsealed an indictment against seven Iranian nationals on Wednesday, charging that the men launched dozens of denial of service attacks against targe...
Just days after accusing Syrian hackers of a wide range of crimes, US Attorney General Loretta Lynch unsealed an indictment against seven Iranian nationals on Wednesday, charging that the men launched dozens of denial of service attacks against targe...
America accuses Iran of hacking the dam, cyber-squirrels rejoice
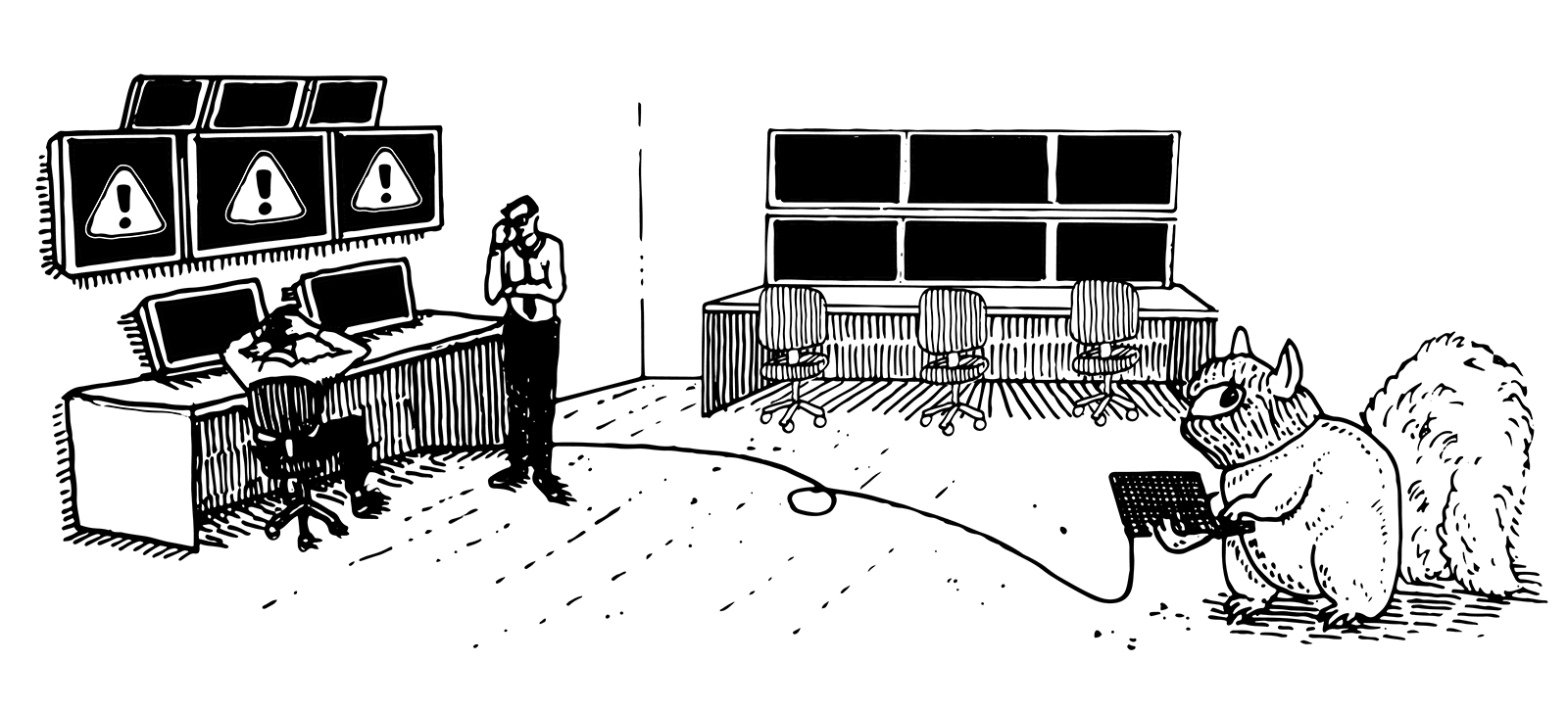 As cyber-geddon stories go, Middle Eastern countries hacking into US dams or power grids and making stuff go haywire sounds like the plot for a not-so-subtly racist Hollywood scare flick. But that's the story we got when news outlets, citing unnamed...
As cyber-geddon stories go, Middle Eastern countries hacking into US dams or power grids and making stuff go haywire sounds like the plot for a not-so-subtly racist Hollywood scare flick. But that's the story we got when news outlets, citing unnamed...
This is The Best Time To Launch A Cyberattack
Recommended Reading: Stuxnet’s more dangerous precursor, fake memories and more
Recommended Reading highlights the best long-form writing on technology in print and on the web. Some weeks, you'll also find short reviews of books dealing with the subject of technology that we think are worth your time. We hope you enjoy the read.
Stuxnet's Secret Twin (4,176 words)
by Ralph Langner, Foreign Policy
Stuxnet is a pretty nasty nasty customer, especially if you happen to be a centrifuge used in the enrichment of uranium. Amazingly, the story of the first publicly acknowledged cyber weapon keeps getting more and more interesting. Ralph Langner has spent the last several years poring over code and other details of Stuxnet's history and discovered there was an earlier version of the virus, that was even more destructive than the one unleashed on Iran's nuclear facilities. Instead of putting the centrifuge's motors in overdrive, it over pressurized them by closing valves designed to allow gas out. It sounds like a perfectly logical avenue of attack, until you realize that the potential for truly catastrophic failure would have quickly blown Stuxnet's cover.
Symantec: work on Stuxnet worm started two years earlier than first thought
Most of us think we know the tale of Stuxnet: it's a possibly government-sponsored worm that played havoc with Iranian centrifuges in 2009, setting back the country's uranium enrichment program without involving any traditional weapons. Researchers at Symantec, however, now claim there's an untold narrative. They've discovered a Stuxnet 0.5 version that may have been in development or active as soon as November 2005, two years before the commonly accepted timeline. It first surfaced on trackers in November 2007, and would have created wider-ranging chaos at Iran's Natanz nuclear facility by closing vital pressure valves instead of using the subtler centrifuge technique.
Symantec also noticed that this pre-1.0 malware shares traits with the Flamer code base, putting it in the context of an even larger effort than seen so far. Moreover, it would have required extensive knowledge of the Natanz infrastructure -- this was no casual attack, according to the researchers. While we may never know exactly what prompted the revamp, IAEA evidence suggests that Stuxnet wasn't truly effective until the better-known version came into play. We mostly know that modern cyberwarfare had its fair share of growing pains -- and that it's not as fresh-faced as we assumed.
Filed under: Internet
Via: Ars Technica
Source: Symantec (PDF)

